In 2014, a friend of mine lost 12 Bitcoins.
Not because the blockchain failed.
Not because Bitcoin crashed.
But because his wallet security was weak.
Fast forward to 2026 — crypto wallets are no longer simple key storage apps. They are complex, multi-layered security systems designed like digital vaults.
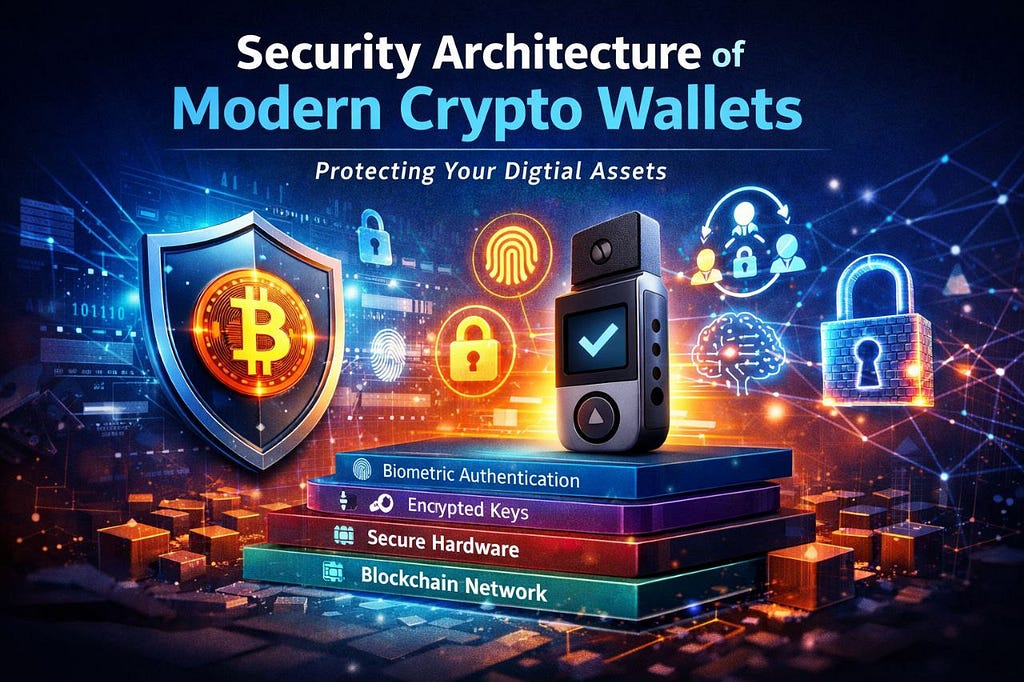
Today’s modern crypto wallet security architecture combines cryptography, hardware isolation, biometric protection, AI monitoring, and decentralized authentication to protect billions of dollars in assets.
If you’re building or investing in a crypto wallet product, understanding this architecture isn’t optional — it’s survival.
Let’s break it down.
Security architecture of a crypto wallet refers to the structured framework of technologies, protocols, encryption layers, and authentication systems used to protect private keys and digital assets.
At its core, every wallet protects one critical thing:
The Private Key.
Because whoever controls the private key controls the crypto.
Modern wallets now use layered protection including:
Let’s explore each layer.
1. Private Key Management (The Heart of Wallet Security)
A crypto wallet does NOT store coins.
It stores:
Modern wallets use:
Examples:
Cold wallets isolate private keys in secure chips (Secure Element).
Hot wallets encrypt keys locally before syncing.
Modern wallets use HD wallet architecture (BIP-32, BIP-44 standards).
This means:
If someone steals one address, others remain safe.
This is why modern wallets generate:
12-word or 24-word recovery seed phrases.
These phrases follow BIP-39 mnemonic standards.
Multi-signature wallets require multiple approvals before funds move.
Example:
This architecture protects against:
Used heavily by institutional crypto platforms.
Modern mobile wallets use:
For example:
Private keys never leave the hardware-protected chip.
Even if malware infects the phone, keys remain isolated.
Modern wallets now integrate:
This reduces:
Wallet security today is no longer just cryptographic — it’s behavioral.
6. Smart Contract Interaction Security
With DeFi growth, wallets interact with smart contracts daily.
Security features include:
Wallets now warn users before signing suspicious approvals.
Modern wallets use:
Private keys NEVER touch centralized servers.
This architecture ensures:
Even the wallet company cannot access user funds.
Here’s where things get advanced.
AI systems now monitor:
Machine learning models detect fraud before the transaction completes.
This is becoming standard in enterprise-grade crypto wallet platforms.
Security isn’t only about protection.
It’s also about recovery.
Modern wallets implement:
Example:
The architecture ensures no single point of failure.
Future-ready wallets integrate:
Instead of passwords, users sign cryptographic messages.
This eliminates:
What makes a crypto wallet secure?
A secure crypto wallet uses encrypted private key storage, hardware isolation, multi-factor authentication, HD wallet structure, and secure transaction signing to protect digital assets.
Is a hardware wallet safer than a software wallet?
Yes. Hardware wallets like Ledger store private keys offline, reducing exposure to online attacks.
Can crypto wallets be hacked?
Wallet apps can be compromised if security is weak. However, properly encrypted wallets with secure enclave protection and seed phrase isolation are extremely difficult to hack.
What is the most important part of wallet security?
Private key management and seed phrase protection are the most critical components.
The future includes:
Modern crypto wallet architecture is evolving from “storage app” to “autonomous security system.”
The security architecture of modern crypto wallets is not a single feature — it’s a multi-layered defense system.
From private key encryption
To hardware isolation
To AI fraud detection
To decentralized identity
Everything is designed around one mission:
Protect the private key at all costs.
If you’re building a wallet platform today, security must be the foundation — not an add-on.
Because in crypto, trust is not given.
It’s engineered.
Security Architecture of Modern Crypto Wallets was originally published in Coinmonks on Medium, where people are continuing the conversation by highlighting and responding to this story.