
Lazarus Group has launched a new cyberattack campaign that tricks employees into infecting their devices.
Lazarus Group is currently using fake meeting invitations to gain access to company systems. Their goal is to steal credentials, sensitive data, and financial information from businesses.
The attack starts with a message sent through Telegram, usually from a compromised or trusted contact. Victims are then invited to join a meeting that appears to be hosted on either Zoom, Microsoft Teams, or Google Meet.

Source: any.run
When the user clicks the link, they are taken to a website that looks real. The fake site shows an error message and tells the user to copy and paste a command into their terminal to fix the issue. This step gives Lazarus Group control, because the user runs the malicious command themselves.
This campaign introduces a new macOS malware kit called Mach-O Man. It is designed to avoid detection by using normal system tools and relying on human behavior instead of technical vulnerabilities.

Source: any.run
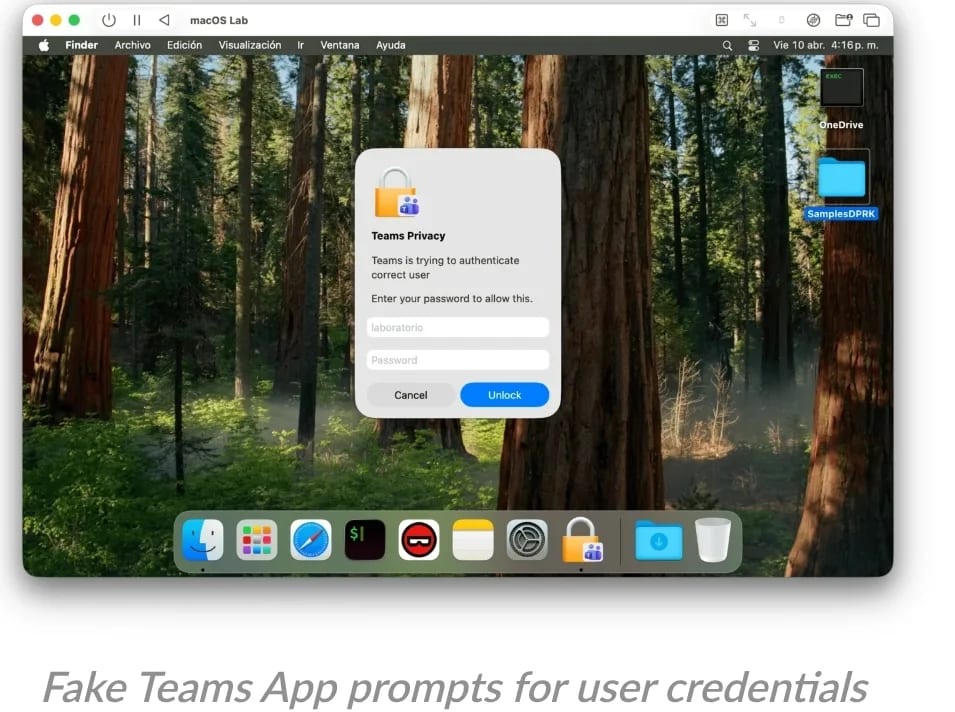
After the command is executed, the malware installs itself in several stages. First, it runs a file that downloads fake applications that look like trusted software. These fake apps repeatedly ask the user for their password, even if the password is correct, and then pretend the process has succeeded.
In the background, the malware collects system details such as device information, running processes, and browser data. Lazarus Group created it in such a way that it targets popular browsers to extract saved credentials, cookies, and extensions.
Also Read: Crypto Bridge Laundering Surges After $290M Lazarus Hack
The attack then creates persistence on the device by installing hidden startup processes. This ensures the malware continues running even after the system is restarted.
Finally, a data-stealing component gathers sensitive information, including macOS Keychain data and stored login details. All this data is packaged into a file and sent back to the attackers using Telegram, which helps the activity blend into normal traffic.
This campaign is hard to detect because it relies on social engineering rather than software flaws. Since users execute the commands themselves, many security systems do not flag the activity as suspicious. Also a single compromised device can give attackers access to an entire organization’s infrastructure.
Also Read: MINA Eyes $0.55 Rally as Token Shows Stability Amid Market Volatility