In a high-intensity market event today, Polkadot ($DOT) experienced a sharp 5% price crash within a mere 5-minute window. The volatility resulted in the immediate wiping of $20 million in market capitalization and triggered the liquidation of over $728,000 in DOT long positions.

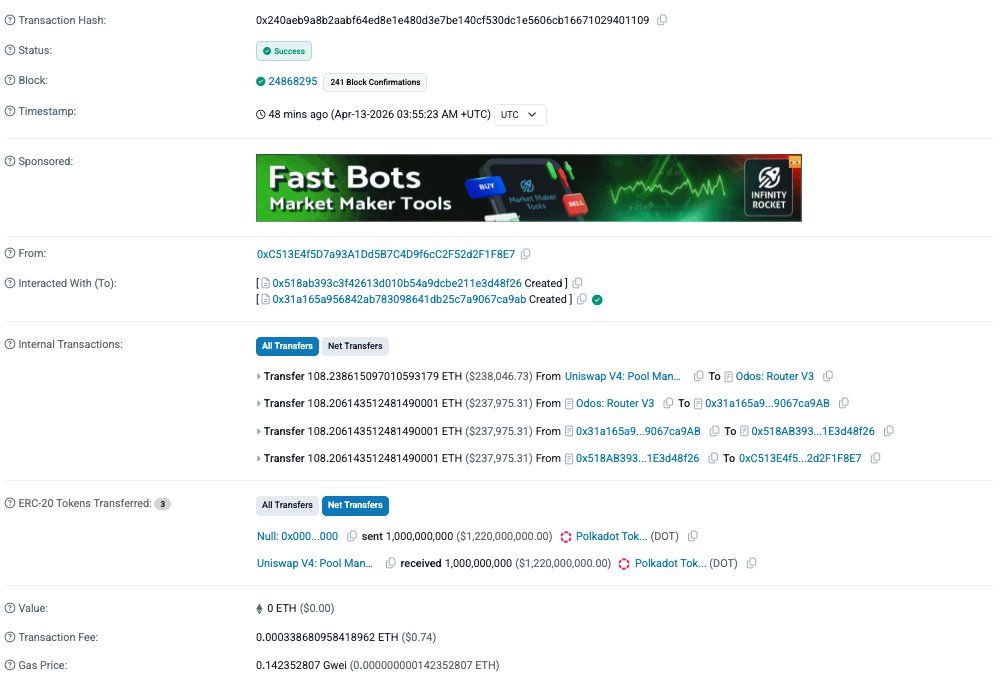
Early reports circulating on social media suggested a direct exploit of the Polkadot main chain. However, on-chain forensics quickly clarified that the vulnerability lies within Hyperbridge, a third-party interoperability protocol connecting Polkadot to Ethereum. The attacker successfully minted 1 billion "fake" wrapped DOT on Ethereum and dumped them into a Uniswap V4 pool, netting approximately 108.2 ETH ($237,000) in a single atomic transaction.
The exploit was not a breach of Polkadot’s core security but a failure in the Hyperbridge architecture. Hyperbridge utilizes the Interoperable State Machine Protocol (ISMP) to facilitate asset transfers. The attack targeted the EthereumHost and HandlerV1 contracts on the Ethereum side of the bridge.
The attacker (address 0xC513...F8E7) executed the following sequence in one transaction:
The source check in the TokenGateway failed because the attacker controlled the MMR root. When you control the root, you control the proof—the security check becomes a tautology.
While the primary panic centered on $DOT, the scope of the exploit was broader. Multiple Hyperbridge-wrapped assets were targeted using the same vector:
It is crucial for investors to understand that native DOT on the Polkadot Relay Chain remains secure. The "crash" was a result of market panic and automated trading bots reacting to the sudden liquidity pool imbalance on Ethereum. Users are encouraged to verify their holdings and check current rates on the Polkadot Ticker Page.
The catastrophe was made possible by two primary architectural weaknesses:
The attacker appears to be a highly sophisticated actor, with wallet history showing preparation dating back over eight months, including the use of RAILGUN for fund obfuscation.