
The Move language, initially built for Meta’s Diem and adopted by Aptos, reshapes how developers approach smart contract safety. Move treats assets as resources, owned, transferable, and impossible to duplicate accidentally. This design eliminates many classical attack vectors but introduces new logic and capability risks that require specialized review.
A Move smart contract audit validates whether on-chain logic, resource management, and module visibility behave safely under all conditions. It’s not a syntax check; it’s a full examination of how design assumptions hold under Move’s ownership model. This article outlines what developers should expect from a professional Move audit, its phases, typical findings, and how to prepare effectively.
Move enforces safety by construction. Every piece of data is either a copyable value or a non-copyable resource, making unauthorized duplication and reentrancy impossible by design.
For auditors, this removes many EVM-era risks, such as reentrancy and overflow, but does introduce some new ones:
Aptos audits focus on confirming that these guarantees hold across all execution paths, not just under normal conditions.

Smart contract auditing involves pre-audit preparation, code review, testing, documentation, remediation, and a final review before deployment.
A Move audit begins with a well-defined scope. Projects typically provide:
A good audit scope covers both core modules (like liquidity pools, token minting, or vaults) and critical dependencies (such as oracle integrations or capability managers). Developers should prepare by running the Move Prover locally to verify basic properties. Doing so shortens audit cycles and helps identify low-hanging issues early.
Common pre-audit findings include:
These are rarely fatal, but they highlight the importance of documenting capability flows and friend declarations clearly before any external review.
Manual line-by-line review remains the audit core. Tools assist, but human reasoning validates business logic and resource integrity.
Auditors trace:
Because Move eliminates reentrancy, emphasis shifts toward state consistency, ensuring no assets remain unclaimed, unlocked, or duplicated through complex flows. In addition, auditors also inspect friend relationships, confirming that only trusted modules gain privileged access and that none can escalate permissions indirectly.
The testing phase combines formal verification and dynamic analysis.
While formal proofs offer mathematical certainty, their accuracy depends on well-defined specifications. Auditors often refine these specs or highlight unverified assumptions for follow-up.
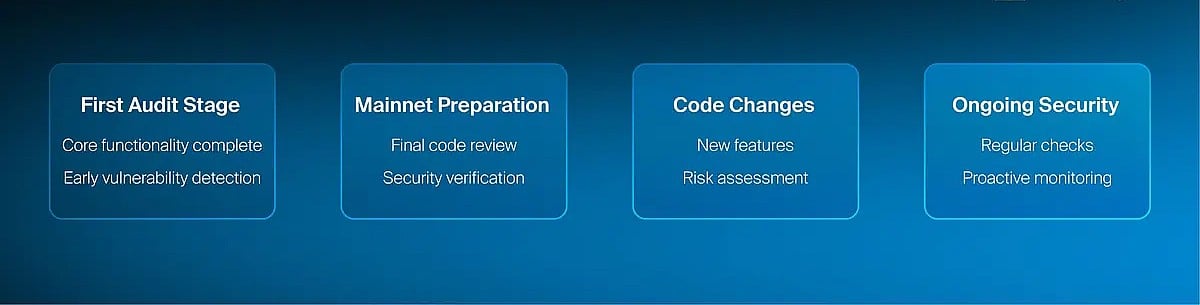
Conducting a smart contract audit is not just a one-time event; it’s a strategic process that should align with key milestones in a project’s lifecycle.
Final reports categorize findings by severity:
Each issue includes description, impact, remediation advice, and relevant code excerpts. A verification round follows remediation, confirming that fixes have been re-audited and redeployed correctly.
Deliverables include:
These artifacts become core proof points for investors, ecosystem listings, and integrations.
“Safe by design” ≠ “audit optional.” Type safety still needs design safety.
Auditors also validate economic correctness and systemic assumptions beyond language safety:
Examples:
Preparation can save weeks of audit time. Developers can adopt a few key habits before submitting code for review:
By following these steps, teams reduce friction and make the audit phase more about refinement than discovery.
Audits have become a trust requirement for Aptos deployments. Foundations and launchpads increasingly require third-party verification before listings or integrations. Beyond compliance, audit insights feed back into shared libraries, improving community-wide security maturity. This cycle, review, disclosure, and refinement form the backbone of Aptos’ growing developer culture.
Even with tools like Move Prover and fuzzing frameworks, human reasoning remains irreplaceable. Security engineers interpret specifications, question assumptions, and uncover systemic risks that automated checks overlook. For instance, a code snippet might pass all proofs yet fail at runtime due to an off-chain oracle discrepancy or mis-specified parameter update. An experienced auditor recognizes such patterns from prior incidents across different blockchains. This human pattern recognition, cross-chain intuition applied to Move’s structured environment, is what differentiates a routine audit from a comprehensive one.
A Move smart contract audit on Aptos is not about proving that “no bugs exist.” It’s about validating that design assumptions and ownership models remain consistent under all conditions. Move’s type system removes many traditional vulnerabilities, but economic, architectural, and privilege-level risks still demand expert verification.
By combining formal proofs, manual reasoning, and adversarial testing, professional audits transform code safety into measurable confidence, helping developers, investors, and users trust the systems they build upon.