TL;DR:
Bitcoin Core secretly patched the first memory security vulnerability in the project’s history, months before publicly disclosing it. The flaw, catalogued as CVE-2024-52911 and classified as high severity, affected all software versions between 0.14.0 and 28.x, and created the possibility that a malicious miner could remotely crash third-party nodes through specially crafted invalid blocks.
The bug corresponds to a *use-after-free* vulnerability in the script validation engine. During block validation, precalculated data stored in cache could be destroyed while a background validation thread was still reading it. Given the underlying mechanism, the exploit not only enabled an abrupt node shutdown, but also left open — though unlikely — the possibility of remote code execution during the resulting abnormal memory state.
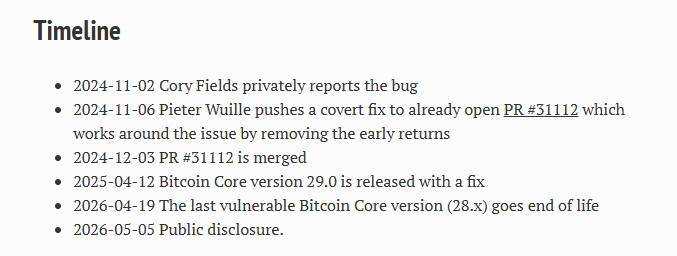
Cory Fields, a researcher at the MIT Digital Currency Initiative, discovered the vulnerability and privately reported it on November 2, 2024. Four days later, Bitcoin Core developer Pieter Wuille implemented a covert fix, deliberately titled “Improve parallel script validation error debug logging” to avoid alerting potential attackers. The fix was incorporated into the repository in December 2024 and distributed with Bitcoin Core v29.0 in April 2025.
Public disclosure only took place once the 28.x version line reached end of life on April 19, 2026. Developer Niklas Gögge noted that this is the first memory security issue recorded in approximately two years of the project’s public security advisory history, and acknowledged Fields’ responsible disclosure.

The deterrent element built into the attack vector also deserves attention: any miner attempting to exploit it would have needed to burn real hashpower on invalid blocks with no reward whatsoever — a guaranteed loss that likely explains why the vulnerability remained dormant in practice.
Bitcoin’s consensus rules were not affected at any point, as the bug was confined to the node software’s memory handling. However, based on estimates from Clark Moody’s dashboard, around 43% of active nodes would still be running versions prior to v29.0 and would remain exposed.