TL;DR:
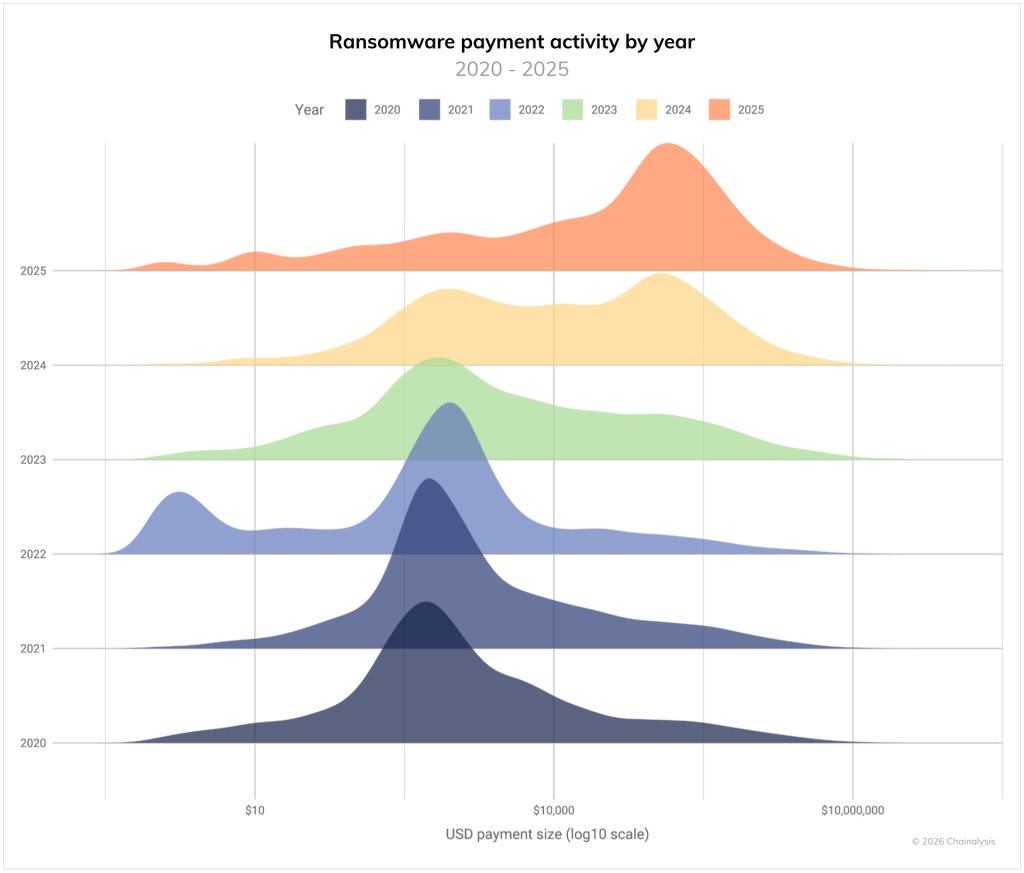
2025 was the most active year in the history of extortive cybercrime, ransomware has expanded deeply across the industry. According to the annual report published by Chainalysis, attacks increased 50% year-over-year, with nearly 8,000 leak events recorded. However, on-chain payments totaled $820 million, an 8% decline from the $892 million estimated for 2024, revealing that there is a growing gap between the volume of attacks and the revenue actually obtained by attackers.
The proportion of victims who paid the ransom reached a historic low, settling at around 28%. The report attributes this trend to improved incident response capabilities, increased regulatory scrutiny and coordinated law enforcement actions against money laundering infrastructure. Corsin Camichel, founder of eCrime.ch, noted that “attackers are working harder for diminishing returns.”
A structural factor explaining the increase in Ransomware attack volume is the sustained decline in the price of access to compromised networks. According to data from Darkweb IQ, the average price fell from $1,427 in early 2023 to $439 in the first quarter of 2026.
This reduction reflects the proliferation of automated tools, artificial intelligence integrations and an oversupply of low-cost access on dark web marketplaces. The result is a more decentralized ecosystem, with up to 85 extortion groups active simultaneously.
Initial Access Brokers —intermediaries who sell access to compromised networks— received at least $14 million in on-chain payments during 2025. Although this figure is modest relative to ecosystem totals, Chainalysis’s analysis indicates that spikes in flows toward these criminals anticipate increases in ransomware payments with a window of approximately 30 days.

Law enforcement agencies are targeting the infrastructure behind ransomware, rather than focusing solely on specific groups. Operation Endgame, coordinated by Europol, the FBI, Germany’s BKA and the UK’s NCA in May 2025, resulted in the seizure of servers and the disruption of malware families used as entry points in multiple campaigns. In addition, OFAC sanctioned hosting provider AEZA Group in July and provider Zservers in February, the latter linked to the LockBit group.
Although payments moderated their growth, the operational and reputational damage from attacks continued to expand. High-profile cases included the attack on Jaguar Land Rover, which generated estimated losses of £1.9 billion, and the exposure of 2.7 million patient records from dialysis company DaVita.