Venus Protocol is dealing with the aftermath of a collateral-manipulation attack tied to THENA’s THE token, an incident that left the BNB Chain lender with bad debt and reignited a familiar DeFi question: how much protection supply caps and oracle guardrails really offer when liquidity is too thin to support the collateral they are meant to defend.
Lookonchain said in a March 15 post that a hacker manipulated THE’s price and exploited Venus on BNB Chain, leaving about $2.18 million in bad debt behind.
The clearer root-source mechanics came from Venus and its risk manager, Allez Labs. Venus said it had identified unusual activity involving the THE pool and was actively investigating, while Allez said the Core Pool was hit by a supply-cap manipulation attack, THE borrows and withdrawals were paused, and several other at-risk markets were restricted as a precaution.
The heart of the exploit was not a simple oracle glitch. It was a position-building strategy that combined low liquidity, delayed price updates, and a way to bypass Venus’s intended supply-cap protections.
According to Allez Labs, the attacker spent months building a large THE position, eventually reaching about 12.2 million THE, roughly 84% of the market’s cap, before the visible attack phase began. On the day of the exploit, the attacker then transferred THE directly to the vTHE contract instead of going through the standard deposit flow, allowing the position to expand to about 53.2 million THE, or roughly 367% of the intended cap.
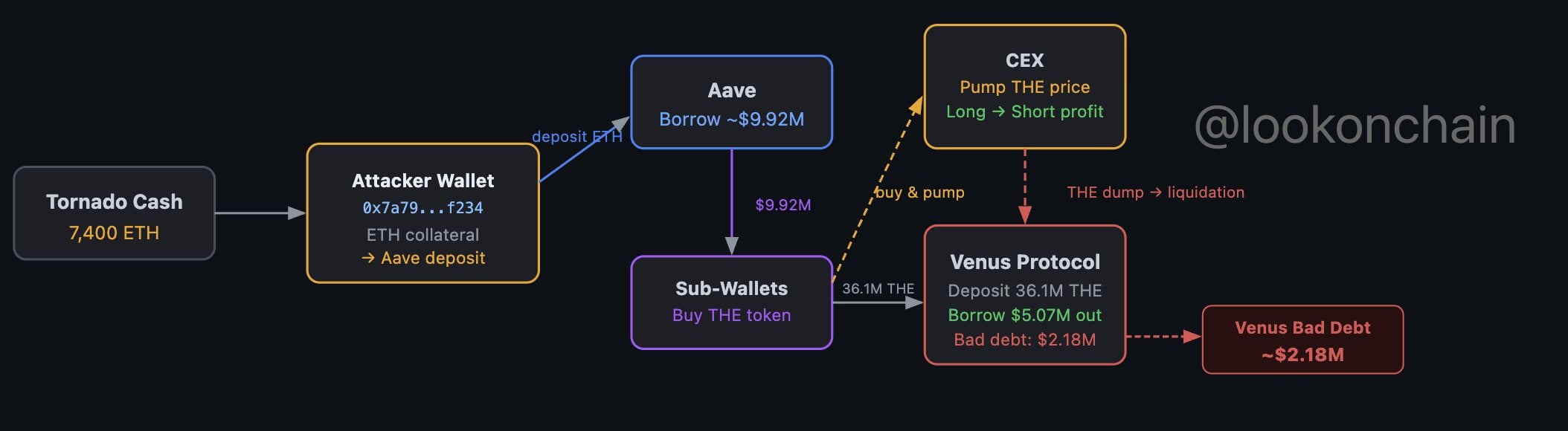
That mattered because it turned a capped collateral market into an uncapped one in practice. Once the attacker had inflated the collateral base, they repeatedly used the same loop: post THE, borrow other assets, buy more THE, wait for the oracle update, and then repeat the cycle while the collateral value kept stepping higher.
This kind of trade only becomes dangerous when the collateral can be pushed around more easily than the protocol can reprice it. That is exactly what happened here.
The attacker was using a token with relatively weak market depth as collateral inside a lending market large enough to let them borrow far more liquid assets against it. Allez said the loop pushed the effective THE price from about $0.27 to around $0.53 before the position later collapsed into liquidation.
At that point, the protocol could seize the collateral, but it could not sell it cleanly at anything close to the marked value because the market was too thin. That is how bad debt appears in lending systems. The protocol may liquidate correctly, but the collateral no longer covers what was borrowed.
At the peak of the position, Allez said the attacker had borrowed a large basket of assets against the inflated THE collateral, including roughly 6.67 million CAKE, 2,801 BNB, 1.97 thousand WBNB, 1.58 million USDC, and 20 BTCB.
That asset mix is important because it shows the exploit was designed to extract more liquid, more portable value against collateral that would be much harder for the protocol to unwind. In other words, the borrower was taking out real marketable assets while posting collateral that could not survive forced liquidation at scale.
Lookonchain’s estimated $2.18 million shortfall is the number likely to stick in headlines because it captures the protocol’s direct residual damage after liquidation. But the deeper issue is not the exact dollar amount. It is the attack pattern.
Venus was not simply hit by volatility. It was hit by a structural mismatch between collateral assumptions and actual market depth. The supply cap was meant to limit exposure. The direct-transfer path let the attacker blow through that cap. The oracle update cadence then gave the position time to grow before reality caught up.
That combination is what makes this more than an isolated hack. It is another reminder that lending protocols can still inherit catastrophic risk when they accept thin assets as collateral and depend on delayed repricing while users with enough capital and patience can slowly build dominant positions.
Venus said the THE and CAKE markets appeared to be affected first, then moved to freeze THE borrows and withdrawals and later reduced collateral factors to zero for several additional markets viewed as vulnerable because of low liquidity and high single-user concentration.
That response shows the protocol is treating the incident as a concentration and collateral-quality problem, not just a one-token anomaly. The message from the risk team is clear enough: if one user can dominate a market with thin liquidity, then the protocol has to rethink not only that asset, but other markets with similar structural characteristics.
The exploit lands at a time when DeFi has become better at handling obvious smart-contract bugs but is still vulnerable to market-structure attacks that exploit design assumptions rather than code failure.
That is why this episode matters beyond Venus. The attacker did not need to invent a new class of exploit. They used a known playbook: accumulate an illiquid asset, use it as collateral, lean on delayed repricing, extract liquid assets, and let the protocol discover too late that its collateral was worth far less than the model implied.
For the market, the immediate result is a damaged Venus market and fresh pressure on THE. For DeFi lending more broadly, the lesson is harsher. Supply caps, oracle windows, and liquidation logic are only as strong as the liquidity reality underneath them. When that reality is too thin, the protocol can still end up lending against a price that does not truly exist.
The post Venus THE Exploit Leaves Bad Debt and Renews BNB DeFi Risk Debate appeared first on Crypto Adventure.